 Breaking into Orbit
Breaking into Orbit

Breaking into Orbit
A 10-module YouTube course from the ethicallyHackingspace (eHs)® community.
120 minutes. Optional 2 CPE credits.
No space background required. No cyber background required.
Breaking Into Orbit is the foundational course of the Space Cybersecurity Operations and Resilience Platform Professional (SCORP2) community, built by the ethicallyHackingspace (eHs)® Team. It introduces the METEORSTORM framework: a converged threat modeling and detection engineering methodology designed for platforms operating across terrestrial, aquatic, aerial, orbital, and deep space environments. Whether you have spent your career in a security operations center, a satellite operations facility, both, or neither, this course starts where you are and builds the common analytical language that every converged platform defender needs.
Who This Course Is For
- Cybersecurity professionals who want to extend their skills to space and converged platform environments without having to earn a degree in orbital mechanics first.
- Satellite operators and space systems engineers who want to formalize their security posture and connect their domain expertise to structured threat modeling and detection engineering methodology.
- Students and career changers with no prior cyber or space background who want to enter one of the fastest-growing and most critically underserved fields in national security and critical infrastructure protection.
- Program managers, mission architects, and leadership who need to understand the methodology their teams will employ without engaging with every technical detail.
- Watch floor analysts, fusion cell leads, and ISAC participants who need a shared analytical language to bridge cross-functional teams defending converged platforms.
What You Will Walk Away With
- A clear understanding of why space, cyber, electronic warfare, and physical threats have converged into a single operational reality that no single existing framework fully addresses.
- Fluency in the METEORSTORM taxonomy: the five-layer shared analytical language (PCE, SEG, SVC, AST, AN) that enables satellite operators, cybersecurity analysts, RF engineers, and mission planners to collaborate within a unified defensive structure.
- The ability to identify and apply all five Primary Capability Environments, all ten Segment tags, all three Service categories, and all six Asset types to real and fictional platform architectures.
- A thorough understanding of a completed Concept of Operations (CONOPS) for a real mission type: a LEO satellite telecommand and telemetry system, expressed in full METEORSTORM taxonomy notation and ready to serve as a threat modeling baseline.
- A thorough understanding of a completed initial threat model overlaying mission-relevant failure concerns onto the CONOPS, with each threat structurally linked to the specific environments, segments, services, and assets it affects.
- A clear roadmap for where to go next: the SCORP2 Cookbook series, the open-source METEORSTORM GitHub repository, the official MISP taxonomy, and the ethicallyHackingspace (eHs)® community.
- Optional 2 CPE credits
Course Format
- 10 modules delivered on YouTube
- Each Module 12 Minutes: 2-minute introduction, 5-minute core content, 5-minute self-paced exercise
- Total runtime: 120 minutes
- Optional 2 CPE credits
- Prerequisites: None
- Cost: Sponsored
Module 1: Space is No Longer a Sanctuary

This module introduces learners to why space cybersecurity has become an urgent operational priority, walking through the five exposure domains: kinetic, non-kinetic physical, electronic warfare, cyber, and environmental, with a real-world example anchoring each one. By the end of this module, learners will be able to articulate why converged defense is necessary and recognize the Viasat KA-SAT incident as the defining case study for the course.
WatchModule 2: Integrating Past, Present, and Future Frameworks
This module introduces learners to the evolving framework landscape, giving genuine credit to the pioneering contributions of MITRE ATT&CK, SPARTA, SPACE-SHIELD, ATLAS, FiGHT, and others while explaining that the landscape will continue to change as new domains, technologies, and adversary behaviors demand new analytical responses. Learners will understand why METEORSTORM was architected with a future-proof ingestion model that absorbs the outputs of any framework, past, present, or yet to be built, and connects them to a unified mission-grounded analytical structure so that every new framework the community produces only makes the collective defense posture stronger.
WatchModule 3: Meet METEORSTORM

This module introduces the METEORSTORM framework by name, acronym, and purpose, unpacking what Multiple Environment Threat Evaluation Of Resources, Space Threats Operational Risk to Missions communicates about the framework's dual analytical focus. Students will learn the five core design principles: Mission First, Structural Traceability, Vendor Agnosticism, Continuous Adaptation, and Convergence by Default, and receive a high-level overview of the five-function cycle that structures every METEORSTORM implementation.
WatchModule 4: The METEORSTORM Taxonomy
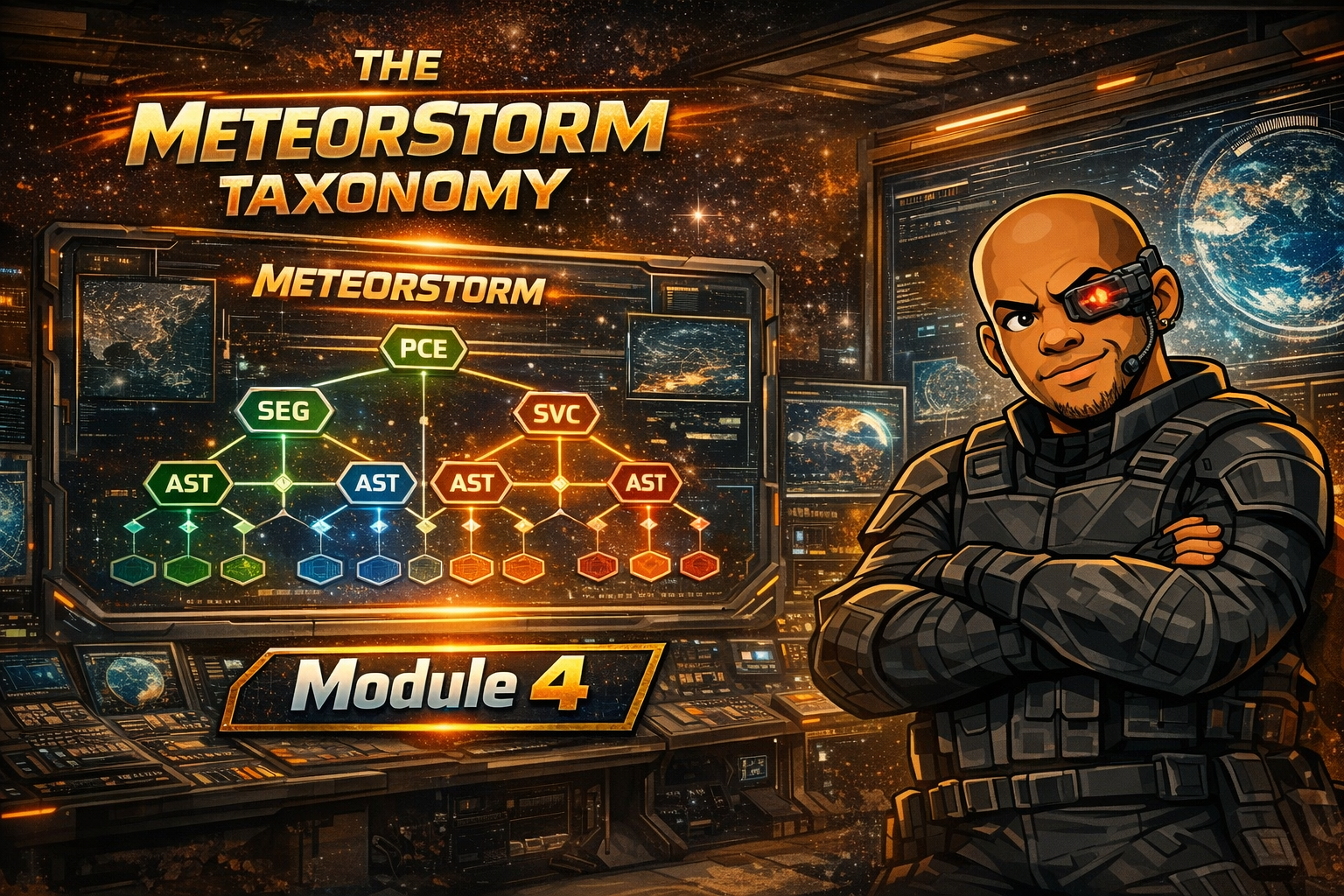
This module provides a deep dive into the five-layer METEORSTORM taxonomy (PCE, SEG, SVC, AST, AN) and the five-component naming convention (Layer, Tag, Category, Ordinal, Description), explaining why a shared analytical language is the connective tissue that makes multi-disciplinary collaboration operationally possible. Learners are introduced to MISP as the reference threat intelligence platform for the taxonomy and to the machine tag format that enables machine-to-machine intelligence sharing across organizational boundaries.
WatchModule 5: Primary Capability Environments (PCE)

This module walks learners through all five Primary Capability Environments: Terrestrial (PCE-TE), Aquatic (PCE-AQ), Aerial (PCE-AE), Orbital (PCE-OR), and Deep Space (PCE-DS), explaining the physical characteristics, operational constraints, and threat-shaping conditions unique to each. Students will understand why environmental context is the foundational layer of the taxonomy and why it is impossible to distinguish natural interference from deliberate attack without first establishing which physical environment a platform occupies.
WatchModule 6: Segments (SEG)

This module covers all ten METEORSTORM segment tags: Launch (SEG-LA), Link (SEG-LI), Ground (SEG-GR), User (SEG-US), Aquatic (SEG-AQ), Low Altitude (SEG-LO), High Altitude (SEG-HI), Near Space (SEG-NE), Space (SEG-SP), and Deep Space (SEG-DE), explaining how segments group platform components by operational role rather than physical location. Learners will understand why the segment vocabulary was designed to reflect an adversary's decomposition mindset, and complete an exercise mapping a fictional LEO constellation to the correct segment tags.
WatchModule 7: Services (SVC)

This module introduces the three METEORSTORM service categories: Control Plane (SVC-CP), Data Plane (SVC-DP), and Hybrid (SVC-HY), explaining why telecommand and telemetry are the two essential control plane services that every space platform depends upon for basic operational survival. Students will learn why services frequently span multiple segments simultaneously and why this distributed nature directly shapes the threat surface that defenders must cover.
WatchModule 8: Assets (AST)

This module covers all six METEORSTORM asset types: Hardware (AST-HW), Firmware (AST-FW), Software (AST-SW), Data (AST-DA), Signal (AST-SI), and Hybrid (AST-HY), walking learners through how to enumerate the concrete elements that implement each service in a ground-link-space telecommand and telemetry architecture. The module emphasizes how thorough asset enumeration replaces vague references to the platform with precise analytical targets that threat modeling and detection engineering require.
WatchModule 9: Reviewing Your First CONOPS
This module walks learners through a completed Function One Concept of Operations for a simplified LEO satellite telecommand and telemetry system, reviewing each layer step by step: mission purpose, PCE enumeration, segment identification, service definition, and asset cataloging expressed in full METEORSTORM taxonomy notation. By the end of this module learners will understand how a real METEORSTORM analytical product is structured, how each taxonomy tag maps to the architecture, and how the finished CONOPS is recorded in MISP using the official taxonomy tags.
WatchModule 10: Reviewing Your First Threat Model

This final module introduces Function Two by walking learners through a completed threat model that overlays mission-relevant failure concerns onto the CONOPS reviewed in Module 9, examining how RF link interference, unauthorized command injection, and telemetry interception are formalized as structured AN-THR threat elements structurally linked to specific platform environments, segments, services, and assets. The module closes with a full course summary, a roadmap to the SCORP2 Cookbook series and open-source METEORSTORM resources, and instructions for claiming optional 2 CPE credits upon completion.
Watch